Hackers have found a new way to steal data using the Bubble platform, a tool originally created to help people make apps without programming. Because these pages look legitimate, common security systems let them go unnoticed.
Recently, cybercriminals have begun exploiting such tools intended for legitimate software development, turning them into an effective vehicle for sophisticated phishing attacks.
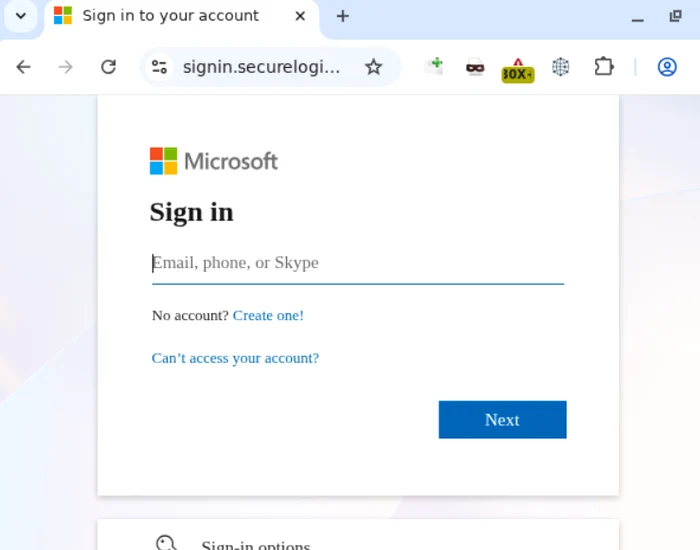
Unlike conventional phishing attacks, which are based on easily detectable malicious links or obvious redirects, the new campaigns use Bubble applications as an intermediary, Kaspersky experts point out. These apps are hosted on the platform’s legitimate infrastructure and use trusted domains like *.bubble.io, which increases their credibility and allows them to bypass traditional security filters. In practice, they function as disguised redirects, leading victims to malicious sites that discreetly collect personal information. In a recent example, victims were ultimately sent to a highly realistic replica of Microsoft’s login page, further protected by a Cloudflare verification layer designed to hide malicious intent.
This method can be integrated into more complex Phishing-as-a-Service (PhaaS) platforms and ready-to-use phishing kits. Such tools allow criminals to conduct highly sophisticated attacks, including real-time cookie interception, Adversary-in-the-Middle (AiTM) attacks that bypass multifactor authentication, and campaigns through legitimate services such as Google Tasks or Google Forms. In addition, modern kits use artificial intelligence to generate phishing emails, geo-localized filters and anti-detection mechanisms to evade security systems. Often these campaigns are hosted on trusted cloud services like AWS to reduce the risk of crashes.
To reduce the risk of exposure to such attacks, specialists recommend several protective measures:
- Training employees to recognize that corporate credentials should only be entered on official and verified platforms.
- Implementing advanced security solutions that block access to known or suspected phishing sites.
- Use of anti-phishing technologies at the email gateway level to limit exposure to malicious messages.
- Constant threat monitoring so organizations can quickly integrate information about new attack techniques into security operations.
As attackers adopt legitimate development tools and trusted cloud services, it becomes increasingly important for organizations to combine user education with advanced protection technologies and continuous monitoring. Only a proactive and integrated approach can prevent the compromise of corporate data and the loss of control over the digital infrastructure.